Terraform helps manage Okta as code, but it doesn’t test changes, clone tenants, track identity drift, or recover from misconfigurations. Safe Configuration Management adds sandbox replication, dependency-aware cloning, governance, monitoring, and point-in-time recovery.
TL;DR
Terraform is valuable for managing Okta configuration as code, but it stops at deployment. It doesn’t replicate tenants, validate changes in a sandbox, track all configuration drift, or restore a known-good Okta state.
Safe Configuration Management adds the missing operational safety layer: sandbox seeding, tenant and object cloning, cross-tenant promotion, ITSM approvals, real-time change monitoring, continuous immutable backups, and point-in-time recovery.
If identity uptime or compliance matters, Terraform alone is not enough.
Table of Contents
- Why Okta Misconfigurations Matter
- Terraform for Okta Configuration (What It Solves)
- The Gaps Terraform Can’t Solve (With Verifiable Sources)
- Safe Configuration Management for Okta (Acsense)
- Comparison Table
- How to Choose the Right Approach
- Conclusion & Next Steps
- FAQs
1. Why Okta Misconfigurations Matter
Okta configuration (apps, policies, groups, MFA, sign-on rules, lifecycle settings) defines the identity fabric your business depends on.
Every change carries risk:
- A single policy mistake can lock out your entire workforce
- A broken MFA or sign-on rule can interrupt authentication
- A misconfigured app can disrupt SSO
- UI-based admin changes can break compliance requirements
To understand how sensitive these objects are, just look at how Okta structures its identity graph in the official APIs:
- Okta Apps API: https://developer.okta.com/docs/reference/api/apps
- Okta Groups API: https://developer.okta.com/docs/reference/api/groups
- Okta Policies API: https://developer.okta.com/docs/reference/api-overview
- Okta Authentication API: https://developer.okta.com/docs/reference/api/authn/
This shows how deeply interconnected Okta’s configuration is — and why misconfigurations ripple across everything.
Teams often try to solve this with Terraform.
But:
Okta is not infrastructure — it’s the identity control plane.
Terraform can deploy configuration, but it cannot ensure change safety.
Identity teams must still answer:
- Where do we safely test Okta changes?
- How do we clone apps, groups, policies without breaking dependencies?
- How do we detect UI or API changes made outside Terraform?
- How do we compare sandbox vs production?
- How do we recover instantly when someone breaks a rule or policy?
This is exactly what Safe Configuration Management solves.
For deeper context, see:
👉 IAM Resilience overview: https://acsense.com/solutions/iam-resilience
👉 Okta configuration management: https://acsense.com/blog/managing-okta-configurations
2. Terraform for Okta Configuration (What It Solves)
Terraform brings infrastructure-as-code discipline into Okta:
- Declarative HCL
- Git workflows
- CI/CD pipelines
- Repeatability
- Consistency for supported object types
Teams with strong IaC maturity benefit greatly.
But Terraform is limited to the capabilities listed in its Okta provider resources:
🔗 Terraform Okta Provider Resources:
https://registry.terraform.io/providers/okta/okta/latest/docs/resources
If it isn’t listed here, Terraform cannot manage it.
3. The Gaps Terraform Can’t Solve
Every gap below is backed by official Terraform documentation.
Gap 1: Terraform Cannot Clone or Replicate an Okta Tenant
There is no resource in the Okta provider for:
- sandbox replication
- tenant cloning
- point-in-time environment duplication
Verification:
🔗 https://registry.terraform.io/providers/okta/okta/latest/docs/resources
Gap 2: Terraform Cannot Clone Dependency Chains
Okta objects depend on each other (apps → groups → policies → MFA rules).
Okta APIs show dependency-heavy objects:
- Apps: https://developer.okta.com/docs/reference/api/apps
- Groups: https://developer.okta.com/docs/reference/api/groups
Terraform doesn’t detect or replicate dependencies.
It only knows what you explicitly define.
Verification:
🔗 https://registry.terraform.io/providers/okta/okta/latest/docs/resources
Gap 3: Terraform Cannot Compare Environments
Terraform drift detection works only for resources it manages and only when running terraform plan.
Terraform’s state model explicitly confirms this:
🔗 https://developer.hashicorp.com/terraform/language/state/purpose
🔗 https://developer.hashicorp.com/terraform/language/state
This means Terraform cannot compare:
- Prod vs sandbox
- API/UI changes vs TF-managed state
- Admin changes vs code
- Historical config vs current tenant state
Gap 4: Terraform Cannot Provide Change Governance
Terraform has no:
- approval workflows
- peer review enforcement
- ITSM integration
- audit trails
- visibility into non-TF changes
Verification:
🔗 https://developer.hashicorp.com/terraform/language/state/purpose
For governance requirements (SOC 2, ISO27001, NIS2, DORA), infrastructure-as-code alone cannot satisfy auditors.
Gap 5: Terraform Cannot Recover from Misconfigurations
Terraform offers no recovery, because:
- Terraform state is not a backup
- There is no restore capability
- No snapshot capability
- No tenant rollback
- No standby tenant
Terraform’s docs confirm state is not a recovery mechanism:
🔗 https://developer.hashicorp.com/terraform/language/state/purpose
If something breaks in Okta, Terraform cannot fix it.
For true recovery, see:
👉 https://acsense.com/solutions/okta-disaster-recovery
4. Safe Configuration Management for Okta (Acsense)
Safe Configuration Management provides identity-specific safety Terraform lacks.
✔ Multi-Tenant Management
Manage all Okta tenants from a single control plane.
✔ Sandbox Seeding (Full Tenant Replication)
Create production-equivalent sandboxes instantly.
✔ Tenant Cloning (Current or Point-in-Time)
Clone your environment as-is — or clone any historical known-good configuration.
✔ Object Cloning (Dependency-Aware)
Clone apps, groups, or policies with dependency resolution.
✔ Cross-Tenant Promotion
Safely promote verified changes to production.
✔ ITSM Approvals & Peer Review
Integrate ServiceNow/Jira approval flows.
✔ Change Monitoring & Auditability
Track all changes across all tools — with versioning + audit logs.
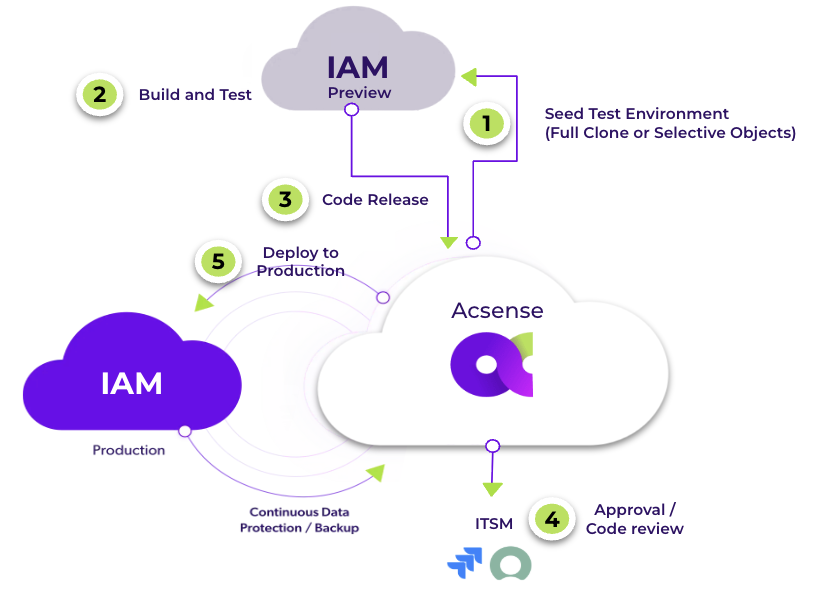
Resilience & Recovery
✔ Continuous, Immutable Backups
Backups that cannot be altered or deleted.
✔ Point-In-Time Recovery
Undo misconfigurations instantly.
✔ Standby Tenant Pattern
Maintain an always-ready fallback Okta tenant.
✔ Compliance Evidence
Generate SOC 2, ISO 27001, NIS2, and DORA reports.
5. Comparison Table:
Terraform vs Acsense Configuration Management
| Capability | Terraform | Safe Configuration Management (Acsense) |
|---|---|---|
| Approach | IaC | IAM Resilience + Configuration Control |
| Multi-Tenant | No | Yes |
| Sandbox Replication | No | Yes |
| Tenant Cloning | No | Yes |
| Object Cloning | No | Yes (dependency-aware) |
| Cross-Tenant Promotion | Scripted | Ordered + Verified |
| Change Monitoring | TF-only | Full IAM visibility |
| Approvals | No | Yes |
| Backups | None | Continuous Immutable |
| Recovery | Manual | PIT + Standby Tenan |
6. How to Choose the Right Approach
Terraform is enough if:
- You only need code-based configuration
- You accept manual validation
- You accept manual rebuilds
You need Safe Configuration Management if:
- You run Okta in production
- You care about uptime
- You need compliance
- You must test changes safely
- You require recovery
- You operate across multiple tenants
7. Conclusion & Next Steps
Terraform helps automate Okta configuration — but Okta requires more than deployment.
It requires identity safety.
Terraform cannot:
- clone tenants
- replicate sandboxes
- detect non-TF drift
- enforce approvals
- or recover a known-good state
Safe Configuration Management fills those gaps and protects the identity control plane.
👉 Schedule a demo:
https://acsense.com/contact-us
FAQs
Can Terraform clone an Okta tenant?
No — Verification:
https://registry.terraform.io/providers/okta/okta/latest/docs/resources
Does Terraform detect misconfigurations made in the Okta UI?
No — Terraform only detects drift in its own state.
https://developer.hashicorp.com/terraform/language/state/purpose
How does Safe Configuration protect Okta?
By adding sandbox replication, tenant cloning, approvals, monitoring, backups, and recovery.
https://acsense.com/platform/change-management
Can Terraform recover Okta after an outage?
No — Terraform has no recovery mechanism.
https://acsense.com/solutions/okta-disaster-recovery
