MGM Resorts Cyber Attack Looks Like Ransomware
MGM Resorts, an emblem of luxury and entertainment, suffered a major operational setback this week, paralyzed by a cyber attack.
As recognized by Forbes, this assault, attributed to the notorious ALPHV/BlackCat ransom gang, disrupted both the casino floors and MGM’s digital infrastructure. Renowned establishments like the Aria, Bellagio, Luxor, MGM Grand, and Mandalay Bay saw their websites taken offline.
According to recent reporting by Las Vegas Review Journal MGM Resorts International could be losing between $4.2 million and $8.4 million in daily revenue and around $1 million in cash flow every day it’s under a cyberattack, a gaming industry analyst said in a Sunday report to investors.
This incident, while devastating, isn’t the first cybersecurity challenge to confront MGM Resorts.
In 2019, the company fell victim to a data breach that impacted approximately 10.6 million people.
A Comprehensive Timeline of the Events (as Reported by Cyber Security Hub):
August 27: A ransomware attack is launched against Caesar’s Palace by hacking gang Scattered Spider. The hotelier allegedly pays $15 million to hackers. This gang is later linked to the MGM Resorts cyber attack.
September 11: MGM Resorts puts out a statement saying a “cyber security incident” has affected some of the company’s systems. An investigation into the cyber attack is launched and the relevant authorities contacted.
September 12: MGM Resorts makes a second statement reporting that all “resorts including dining, entertainment and gaming are still operational” and that its guests “continue to be able to access their hotel room and [its] Front Desk is ready to assist our guests as needed”.
September 12: Guests report a number of issues with MGM Resorts’ online booking system and casino. The company’s main website is reported as being down.
September 13: VX Underground, host of “one of the largest collection of malware source code, samples, and papers on the internet”, makes a post on X saying the MGM cyber attack was the result of vishing. VX Underground also reports that ransomware gang, ALPHV, were responsible for the attack.
September 13: Sources close to the cyber attack say that the hacking group, Scattered Spider, are responsible for the hack.
September 13: Financial services company Moody’s says the cyber attack may negatively impact MGM’S credit. The company also notes that the cyber security incident highlights “key risks” in MGM’s reliance on technology.
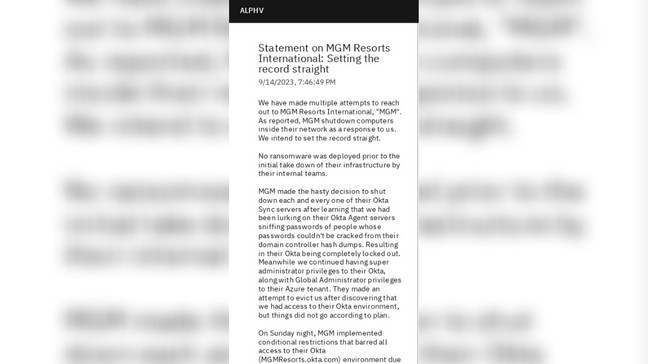
ALPHV/BlackCat Claims Responsibility for the MGM Attack Cyber attack
Amidst the unfolding revelations surrounding the ransomware attacks on MGM Resorts and Caesars Entertainment, the ALPHV/BlackCat ransomware gang has come forward with a statement.
In a detailed statement released on Sept 14 just before 8 p.m. ET, the gang asserted that they had penetrated MGM’s infrastructure the previous Friday. However, they chose to hold off their ransomware deployment until Sunday. Their delay, as they claim, was due to MGM engineers’ non-responsive nature, even after ALPHV repeatedly attempted to reach out or “ping” them without success.
ALPHV/BlackCat, established in 2021, operates under a ransomware-as-a-service (RaaS) model and is associated with several high-profile cyberattacks. With links to notorious groups like Conti, LockBit, and REvil, they’ve carved a niche for themselves by leaking victim data openly on the internet, escalating the urgency for victims to pay ransoms.
Their techniques have been further refined with the introduction of the “Sphynx” variant in 2023, demonstrating their continued commitment to evolving their malicious endeavors.
The Direct Impact on MGM’s Infrastructure
MGM’s ordeal brings to the forefront the imperative nature of business continuity and disaster recovery preparedness.
As The Stack highlights, the pulsating atmospheres of landmarks like Bellagio, Mandalay Bay, and the Cosmopolitan turned ghostly. Slot machines were incapacitated, websites crashed, and guests found themselves locked out due to malfunctioning room keys.
Okta’s Central Role in the Breach
Notably, the core of MGM’s digital turmoil lay within their identity infrastructure, particularly their Okta Sync servers.
The attackers, APLHV, stated, “MGM decided in a rush to shut down these servers,” resulting in a complete lockout.
What was even more alarming, APLHV revealed, “We were actively sniffing on MGM’s networks via Okta,” granting them unprecedented access to sensitive information and system functionalities.
This breach, as described in APLHV’s own words, showcases the inherent vulnerabilities within identity infrastructure. Their ability to monitor communications through Okta underscores the critical need for enterprise-level IAM resilience.
Financial Consequences of Downtime
Highlighting the severe financial implications of such disruptions, Ryan McConechy from Barrier Networks commented in The Stack.
"For every minute the gaming floor was down, MGM was bleeding financially."
While immediate breach responses are vital, a holistic cyber resilience strategy is indispensable
The staggering cost accrued during cyber incidents accentuates the importance of an adept resilience strategy, a principle championed by Acsense.
Additionally, Moody’s also warned that the cyberattack could impact MGM’s credit rating, emphasizing the vulnerabilities of heavily technology-reliant operations.
The attack “highlights key risks” to the company’s operations, given its dependence on technology.
MGM Ransomware Insider Insights
The cyber domain is often shrouded in whispers and insider revelations.
Notably, a user, @LasVegasLocally, privy to MGM insights, intimated the gravity of the situation, casting doubts on the company’s ability to meet payroll commitments, as shared by Stefanie Schappert from Cyber News.
Concurrently, murmurs concerning luxury stalwart Caesar’s Palace surfaced, with suggestions of a whopping $30 million ransom payment to preclude the pitfalls MGM encountered.
Cyber Resilience in Hospitality
In a discussion with Alex Scroxton of Computer Weekly, Erfan Shadabi of Comforte AG delineated the endemic cybersecurity quandaries plaguing the hospitality sector.
With modern businesses heavily reliant on digital conduits, they inadvertently become cybercrime magnets.
Shadabi explained.
"The MGM Resorts incident epitomizes this broad challenge... it's imperative for the tourism industry to earmark resources to fortify its cybersecurity stance."
Resonating with Shadabi’s insights, the learnings from MGM’s predicament harmonize with Acsense’s articulation on cyber resilience’s primacy.
Today’s volatile landscape demands not merely reactive protocols but robust strategies ensuring operational persistence in the face of crises.
This doctrine transcends the hospitality realm, resonating across various sectors.
Taking a Step Back: The Role of Social Engineering and Basics
A profound lesson drawn from both the MGM Resorts incident and last month’s attack on Okta customers is the unmistakable role of social engineering in these breaches.
Cybercriminals often exploit human vulnerabilities, underscoring the need to revert to foundational cybersecurity practices. Acsense emphasizes returning to the basics, which includes emphasizing employee training, safeguarding critical systems through data protection, and implementing disaster recovery solutions.
In the digital age, it’s not solely about the technology we use but the principles we uphold.
Rethinking Cybersecurity Strategies for Resilience
The MGM cyber attack highlights the urgent need for robust IAM resilience in an ever-evolving threat landscape.
As the Okta incidents demonstrated, comprehensive security measures combined with a strong IAM resilience strategy are paramount for business continuity.
Take Proactive Measures for IAM Resilience:
- Access Our Free DRP Guide:
Obtain insights on crafting your IAM recovery strategy here
- Experience a Demo:
See how Acsense’s IAM Resilience Platform can enhance your Okta system’s security here.
Act now to ensure your organization’s resilient future.
