Guest Post: Barry Gordon, Head Coach & Founder at Identity Coach
Okta Terraform ≠ Okta Disaster Recovery
Can You use Okta Terraform to Backup and Recover an Okta Tenant?
This is a common question from teams who rely on Okta Terraform to deploy and configure critical infrastructure.
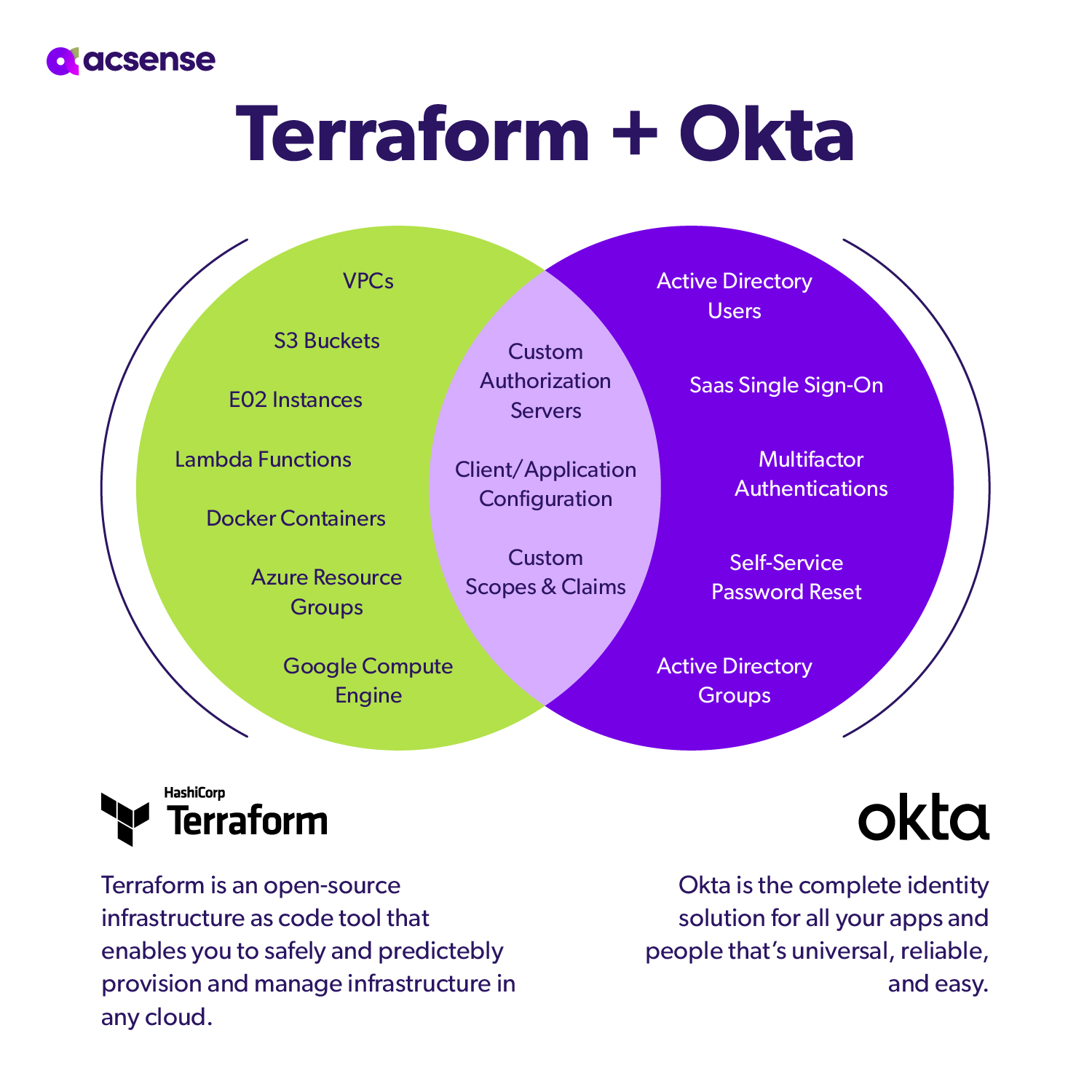
The Terraform Okta provider is an incredible tool for incorporating identity components into your DevOps pipeline. This is a reasonable question but overlooks one key problem: persistence. Unlike a docker container or an EC2 instance, Okta will have data, configuration, and state that will change outside Terraform’s purview. User data, directory-backed objects, and third-party integrations are too dynamic and are impractical to manage with Terraform.
Despite these concerns, I have seen teams attempt to manage them with Terraform to much frustration, disappointment, and wasted hours. The simple fact is that Okta disaster recovery is not an appropriate use case for Terraform.
To answer the original question:
No. Terraform is awesome, but it is not a backup and recovery tool.
Using a purpose-built tool to plan for Okta disaster recovery will save you time, money, and frustration.
When to Use Okta Terraform
How can Okta Terraformbe used effectively?
To allow development teams to add IAM configurations to their development pipeline instead of requiring an Okta administrator. For example, a self-hosted modern web application with a JavaScript front end and API backend. The application uses JSON Web Tokens (JWTs) for authorization to the API.
Custom scopes and claims may be needed to be part of the tokens from the Authorization Server.
These can be configured via Terraform configuration files in a repository, so changes can be tracked and the scopes and claims are ready for use by the application.
The web front end will need a client application configured in Okta to perform authentication, and via Terraform this client and its configuration can be managed via Terraform. As an output, Terraform can place the client credentials into a secrets vault for use by the application. Groups may need to be assigned to this client application in Okta, so new groups can be created at this time, if necessary.
Automating these specific items in Okta can speed up the development and deployment of the application.
What Does a Good Okta Disaster Recovery Solution Look Like?
An Okta tenant can generate a lot of data.
The first step is a backup system that can capture this data consistently and effectively over time.
The ability to query backups to a specific point in time is critical to a successful recovery. Second, comes recovery. All the objects in the backup have relationships that must be maintained. It’s not enough to reimport all the objects in bulk. A specific order of operations on imports must be followed to ensure object relationships are maintained making the recovered state as close to the original as possible.
Building this kind of resilience yourself will take considerable time and resources.
In a Nutshell
Terraform is a powerful tool for helping teams build and manage infrastructure repeatably and consistently; however, it is not a disaster recovery tool. While it would be great to get more out of existing tools, disaster recovery and planning is a distinct domain with its own challenges and solutions. Give disaster recovery concerns the proper due diligence.
Focus on resilience over convenience.
Further Reading on Okta Disaster Recovery:
You may also find these resources insightful: