Enterprise
IAM
Resilience
Bullet-proof your Okta and ensure rapid recovery against cyber threats, misconfigurations and human error.
testimonials
What Our Customers Are Saying…
Digital Adoption Platform

Monday.com










Strategic Partnerships
Together, we address key business challenges, fortifying IAM resiliency. With backup and recovery, we ensure reduced downtime, data integrity, and seamless access. Future-proof your business for 2023 and beyond.
Your Okta System is Vulnerable
Shared Responsibility
Customers are responsible for securing what they host in IAM systems and mitigating risks of misconfiguration, deletion, and tampering.
Human Error
Misconfigurations may cause downtime, lengthy manual recoveries, and unauthorized access, or block legitimate users.
Cyber Threats
Compromised IAM systems present a substantial threat to both availability and security, leading to significant operational and financial risks.
The Okta Disaster Recovery Plan Guidebook
Why Acsense for Okta?
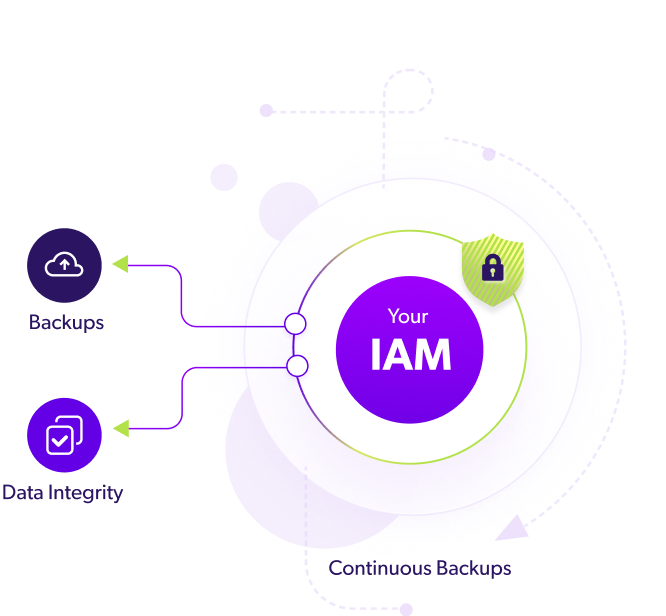
Continuous Data Protection
Safeguard your Okta data with continuous, immutable backups and flexible recovery options, including 1-click and full posture recovery. This robust approach protects against misconfigurations and human errors, ensuring the integrity and continuity of your IAM system.
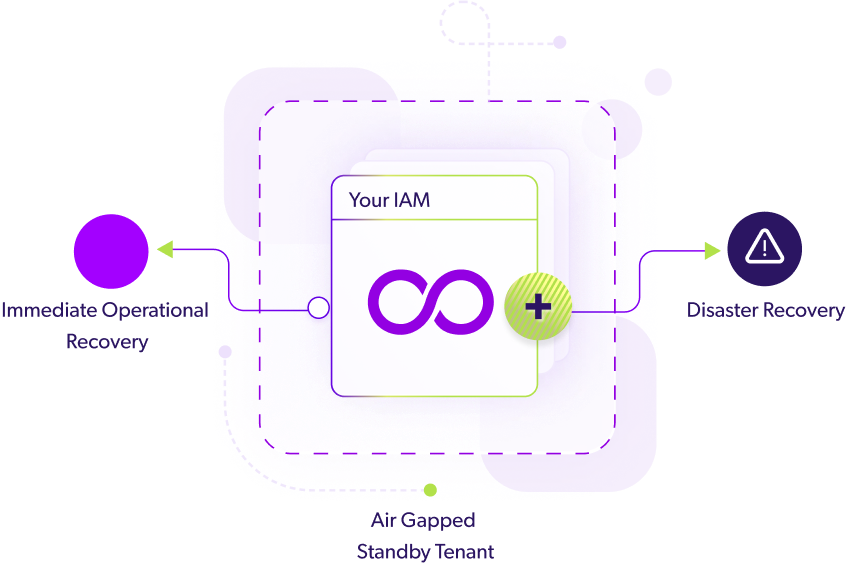
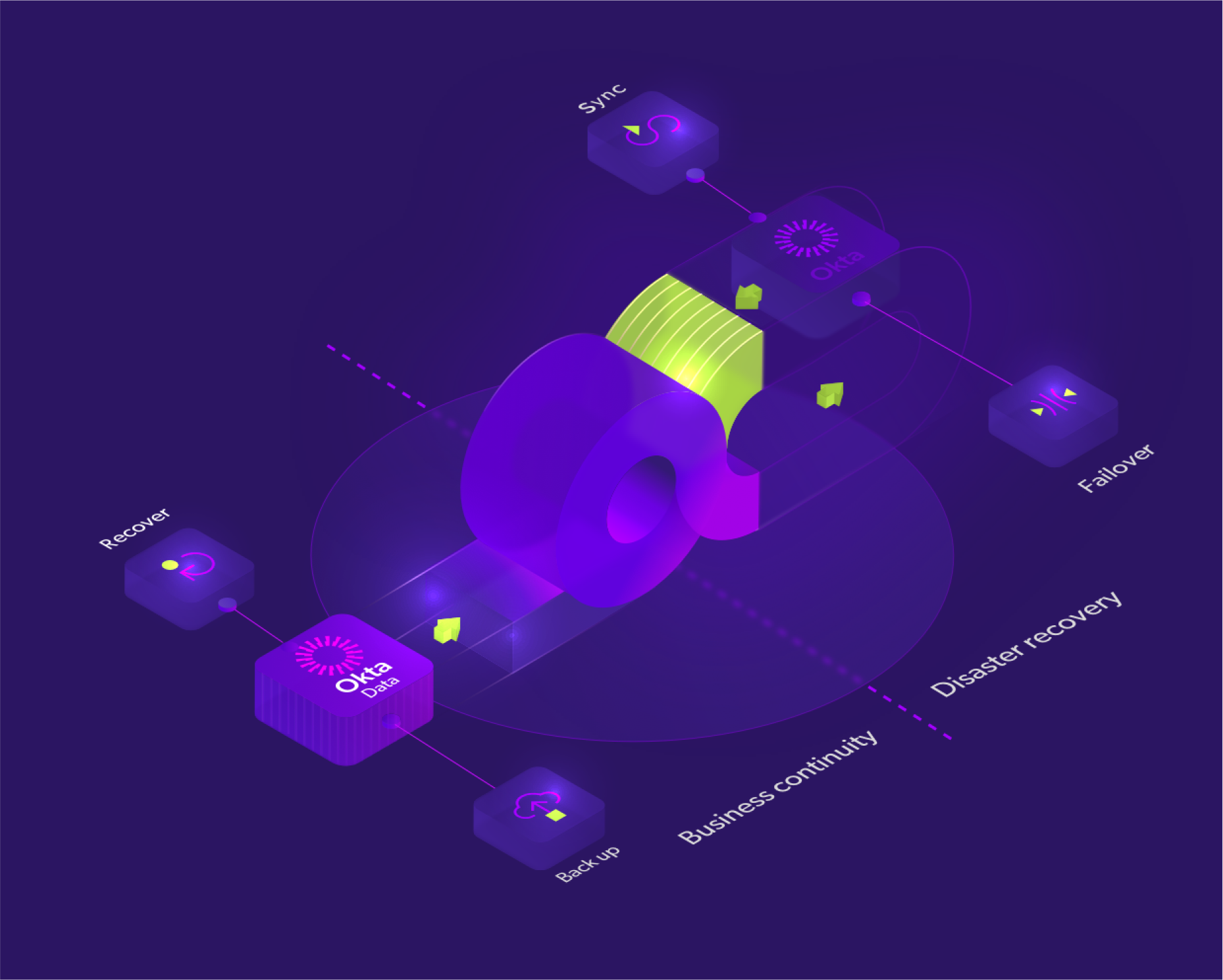
Seamless Disaster Recovery
Quickly rebound from IAM disruptions with our advanced disaster recovery capabilities. Our seamlessly integrated and air-gapped standby tenant, synced with your production environment, ensures immediate operational recovery, reducing downtime and associated costs.
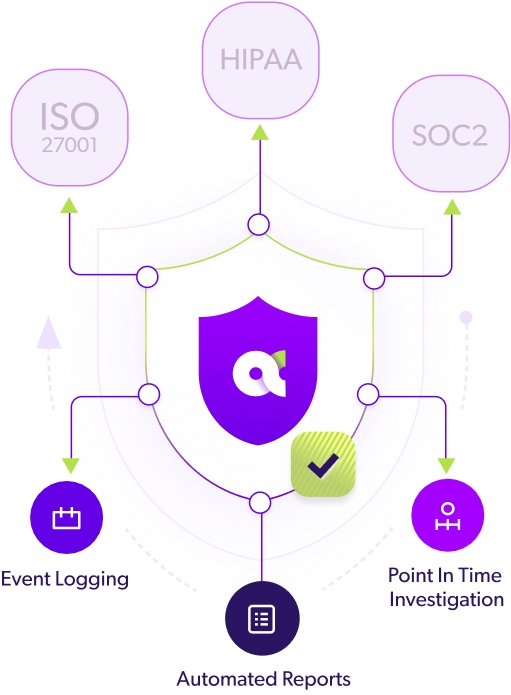
Simplified Compliance
Streamline IAM compliance with a blend of Zero Trust principles and resilient 3-2-1 architecture, catering to standards like HIPAA, ISO 27001, and SOC2. Automated reports, point-in-time recovery options, detailed event logging, and robust posture management not only ensure continuous data integrity but also make audit preparedness efficient and straightforward.
Use cases
Business Continuity
Our access continuity features help maintain operational stability amidst IAM outages caused by breaches or misconfigurations.
Learn More >>
Disaster Recovery
Minimize downtime with a standby backup tenant for quick recovery. Eliminate excess costs associated with complex IAM recovery processes and downtime.
Learn More >>
Compliance
Leverage our real-time IAM change management and investigation capabilities to support your compliance requirements while enhancing security and resilience.
Learn More >>



Use cases
Business Continuity
Our proactive continuity features support Business Continuity teams, maintaining high availability and operational stability amidst IAM breaches, insider threats, or misconfigurationsLearn more >>
Disaster Recovery
Mitigate Okta downtime using a ready backup tenant for Disaster Recovery. Eradicate extraneous costs tied to complex recovery processes and downtime!Learn more >>
Governance Risk & Compliance
Real-time change monitoring enhances your Compliance and Risk teams' IAM compliance, security, and resilience, ensuring robust and compliant business operationsLearn more >>

What's in it For You?
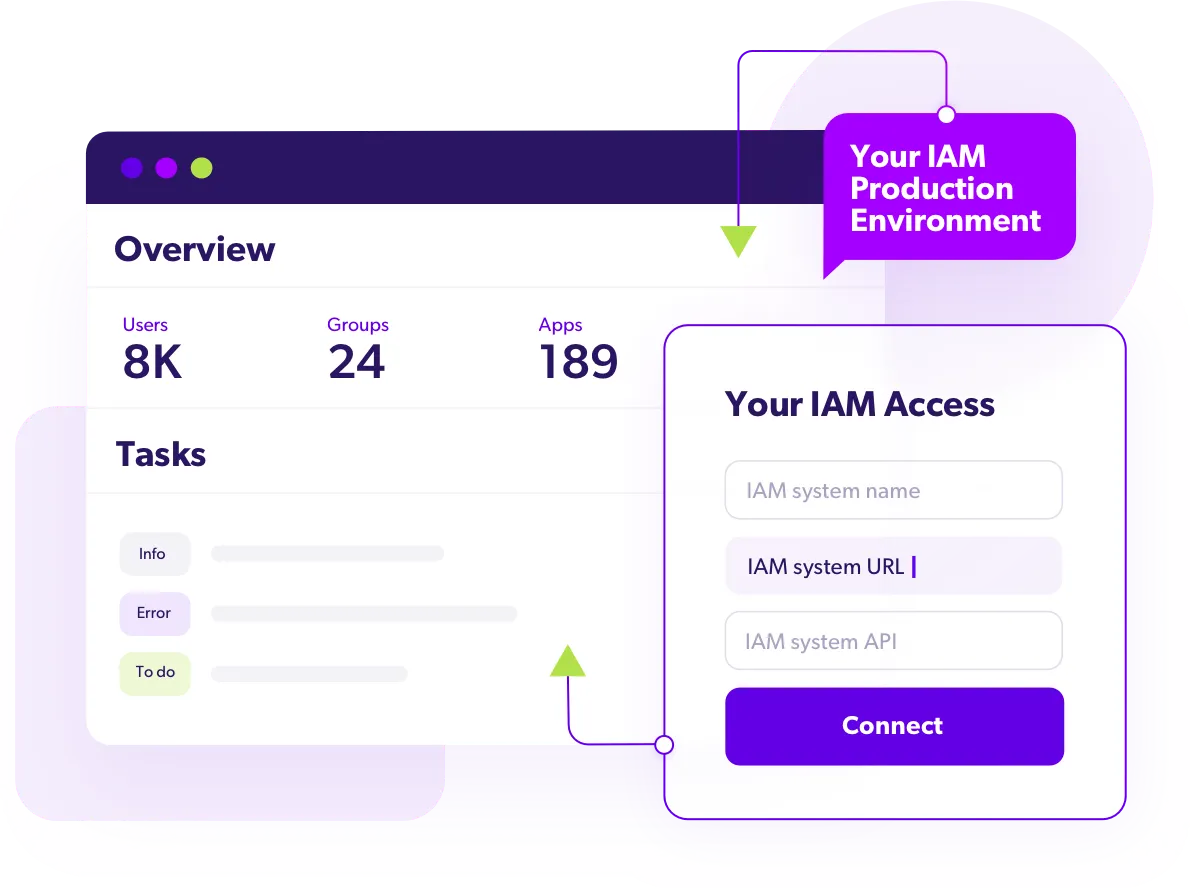
01. Automated Backups
Seamlessly synchronize your Okta tenant in a secured, air-gapped environment, providing continuous protection for all your data and configurations.
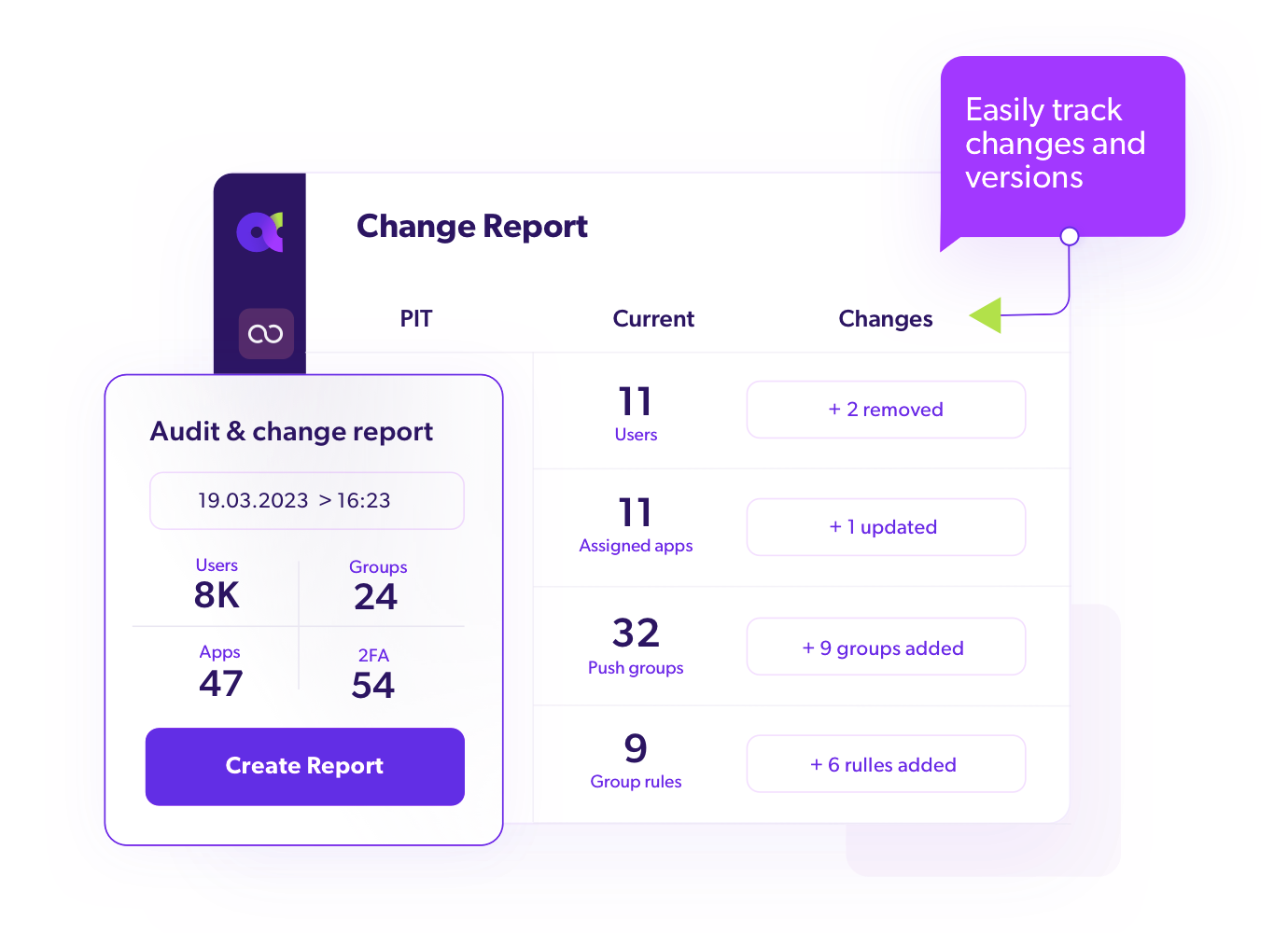
02. Robust Investigation
Assess your Okta’s recoverability by reviewing all changes, configurations and objects between specific points in time.
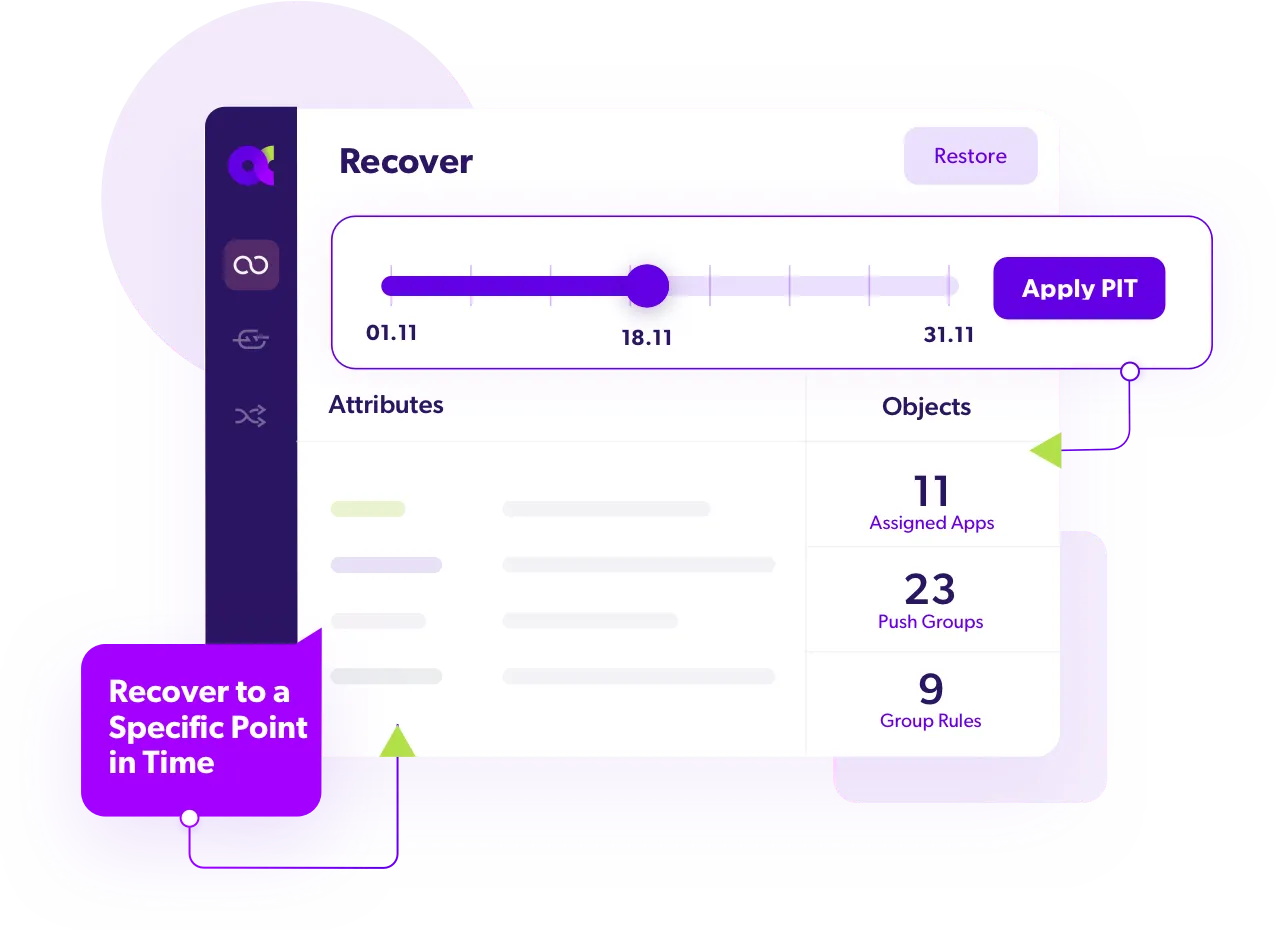
03. Rapid Recovery
Choose any Point-in-Time (PiT) to effortlessly rollback minor data changes or fail-over completely to a secondary Okta tenant.
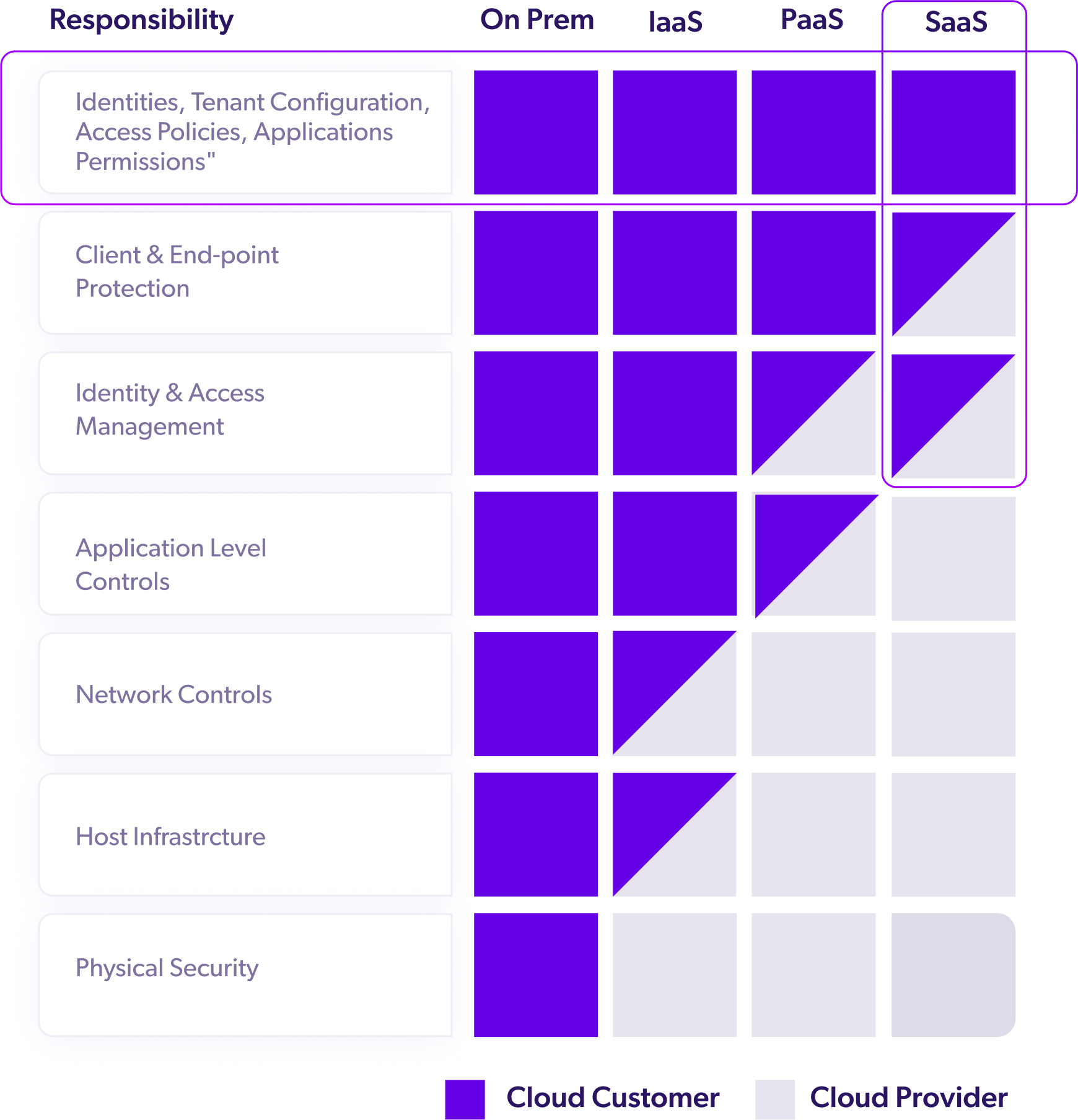
shared responsibility model
Take Back Control of Your IAM Data
Cloud providers, such as Okta, Azure AD, Ping and Forgerock rely on a shared responsibility model. In a nutshell, you are responsible for the information, configuration, rules, etc. that you define within your particular IAM configurations.
Protect Your IAM Investments.
RESOURCE CENTER
From Our Blog
AT&T Admits Huge Data Leak Affects Millions of Customers In recent developments, the cybersecurity community has been abuzz with...
April 1, 2024
Elevate Your IT Operations with Okta Lifecycle Management Managing users within an organization might seem straightforward at first glance....
March 29, 2024
Beyond Prevention in Cybersecurity As the digital landscape continues its rapid evolution, corporate boardrooms are actively adapting their strategic...
March 22, 2024
AT&T Admits Huge Data Leak Affects Millions of Customers In recent developments, the cybersecurity community has been abuzz with...
April 1, 2024
Elevate Your IT Operations with Okta Lifecycle Management Managing users within an organization might seem straightforward at first glance....
March 29, 2024
Beyond Prevention in Cybersecurity As the digital landscape continues its rapid evolution, corporate boardrooms are actively adapting their strategic...
March 22, 2024
Is Your Okta Tenant Truly Recoverable?
Explore insights into the recoverability of your Okta tenant with Acsense.